# RouterOS + tr069 staging process
# Install RouterOS in a virtual machine and connect it to CONTROL
## Overview
This guide walks you through installing RouterOS in a VirtualBox virtual machine and connecting it to CONTROL using the TR-069 protocol.
## Prerequisites
- VirtualBox installed on your system
- Internet connection to download RouterOS files
- Basic familiarity with virtual machine management
---
## Step 1: Download RouterOS
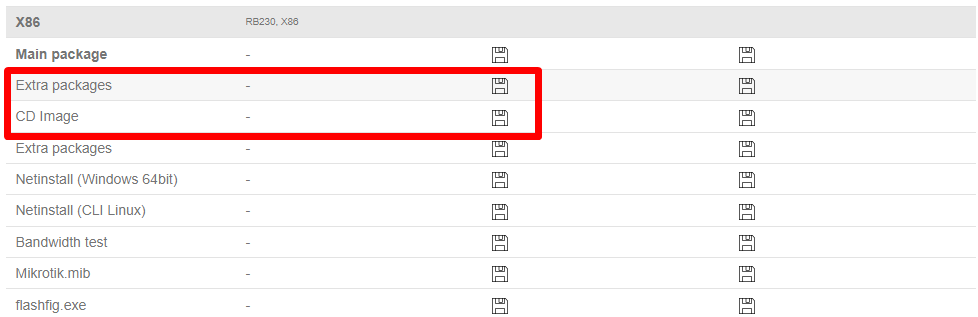
Visit the [MikroTik download page](https://mikrotik.com/download) and download the following files:
- **RouterOS 6.48.6 Long-term x86 ISO image**
- **Extra packages** (contains the TR-069 package)
[](https://docs.zequenze.com/uploads/images/gallery/2022-02/mvEc50XHpoyBlmfN-image-1645563625256.png)
---
## Step 2: Create the Virtual Machine
### Configure VM Settings
1. Open VirtualBox and create a new virtual machine
[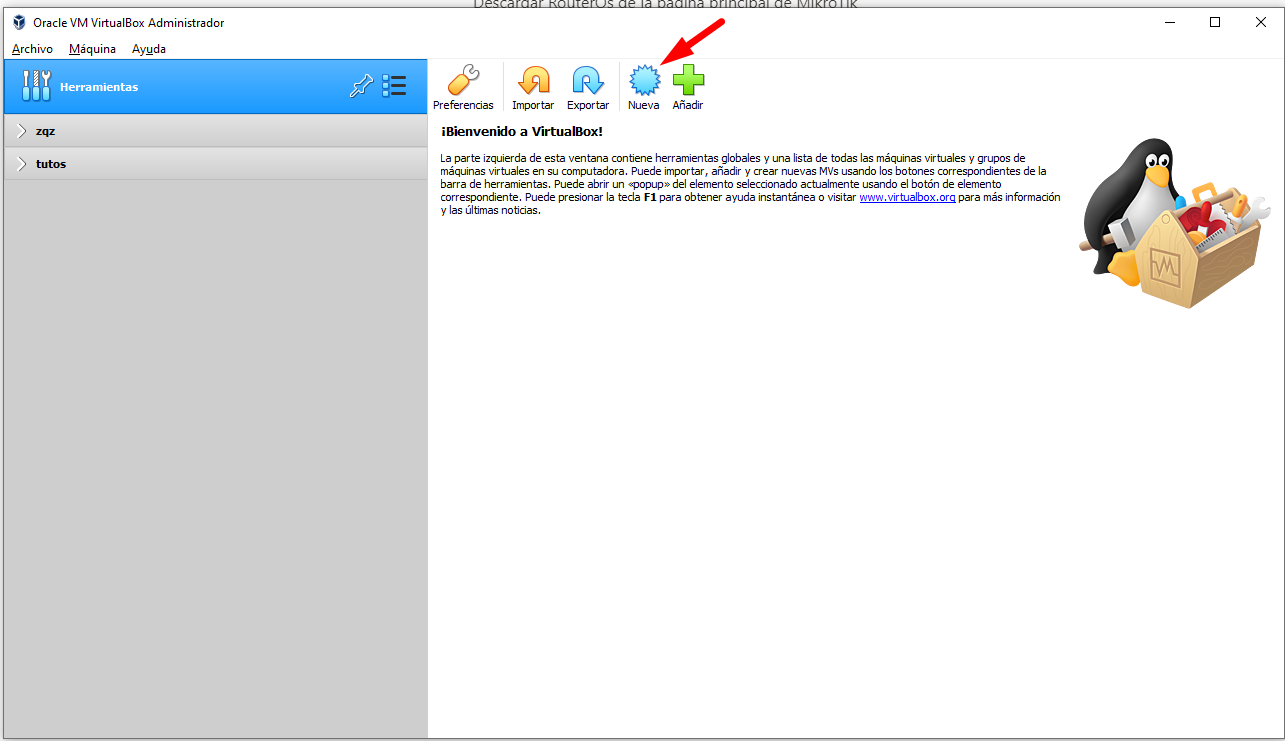](https://docs.zequenze.com/uploads/images/gallery/2022-02/Mv3oDt79NRs9wM3s-image-1645540572569.png)
2. Enter the required information as shown below
[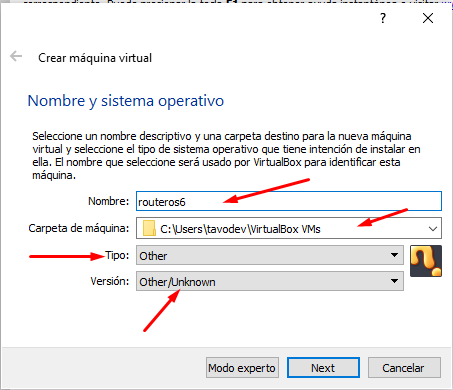](https://docs.zequenze.com/uploads/images/gallery/2022-02/i5esLCZF6cWBfOAg-image-1645540727105.png)
3. Allocate RAM memory (64 MB is sufficient for RouterOS)
[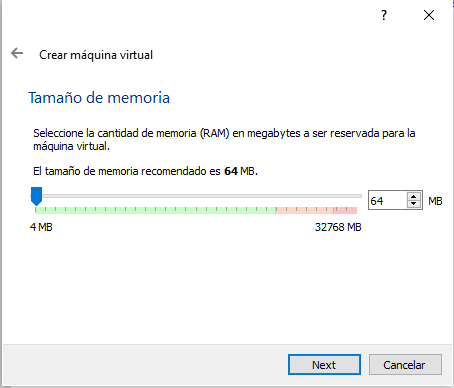](https://docs.zequenze.com/uploads/images/gallery/2022-02/plVH46RssZbjb007-image-1645540756544.png)
4. Create a virtual hard disk with the following settings:
[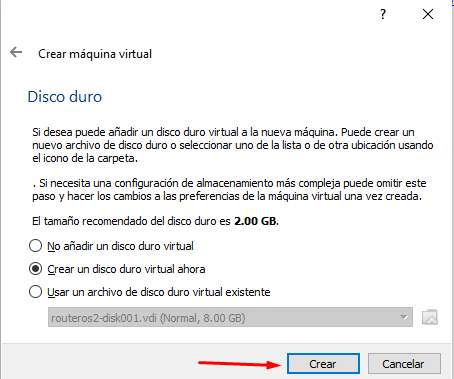](https://docs.zequenze.com/uploads/images/gallery/2022-02/6CfgTqutHS0yi2Ev-image-1645540814470.png)
[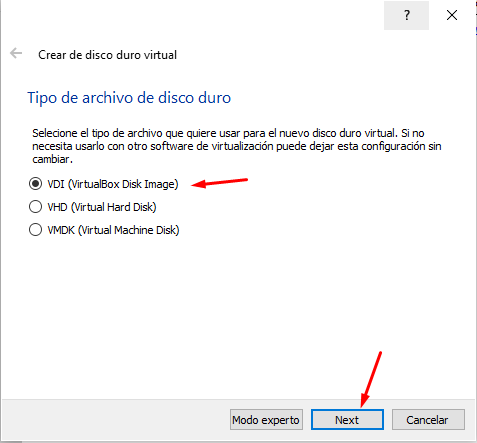](https://docs.zequenze.com/uploads/images/gallery/2022-02/a5wssyxyYP2Qm7H9-image-1645540823381.png)
[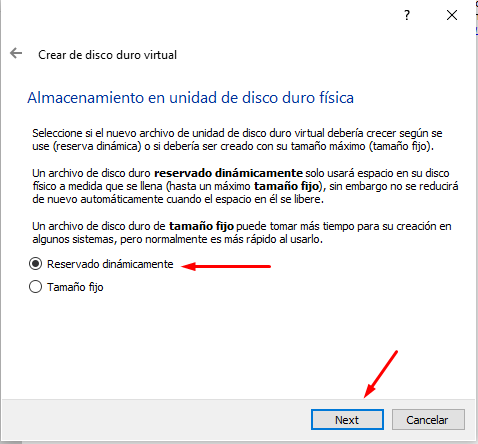](https://docs.zequenze.com/uploads/images/gallery/2022-02/IwXz2cIHSjoozczW-image-1645540843981.png)
[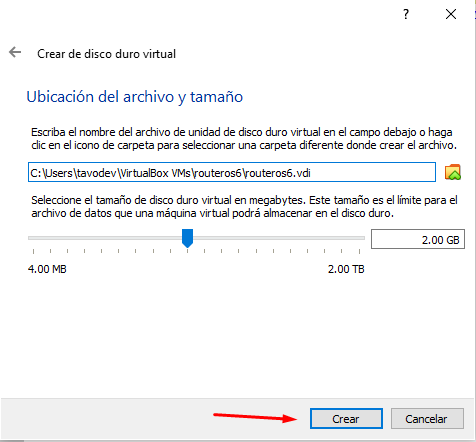](https://docs.zequenze.com/uploads/images/gallery/2022-02/dkQSxSePg1j2hFwM-image-1645540849381.png)
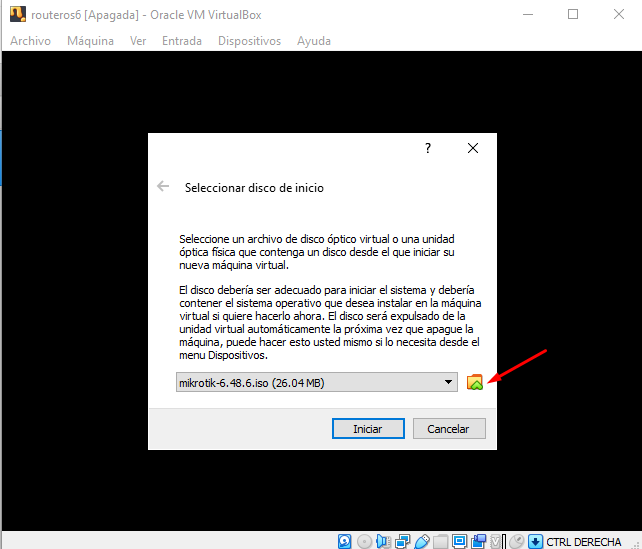
### Configure Network Adapters
5. After the VM is created, add an additional network adapter in the VM settings
[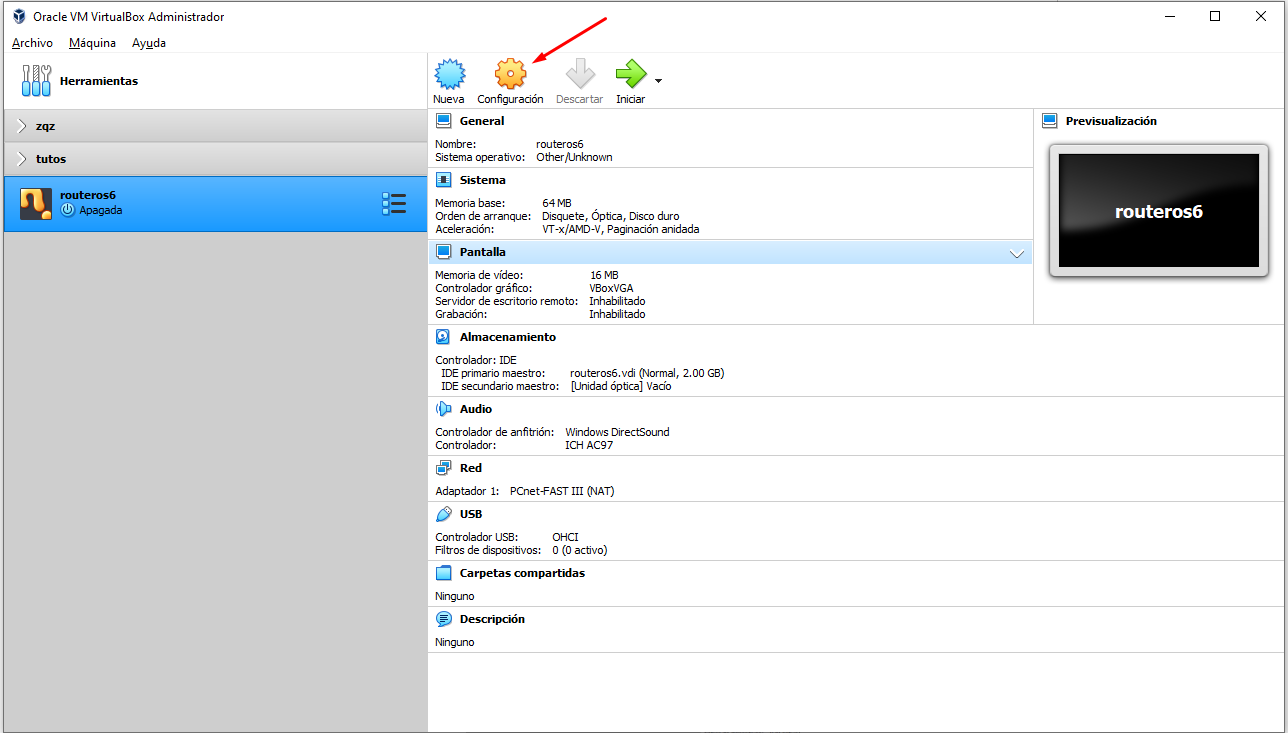](https://docs.zequenze.com/uploads/images/gallery/2022-02/YFc1Xhf8guWfIn2d-image-1645541963736.png)
6. The network configuration should look like this:
[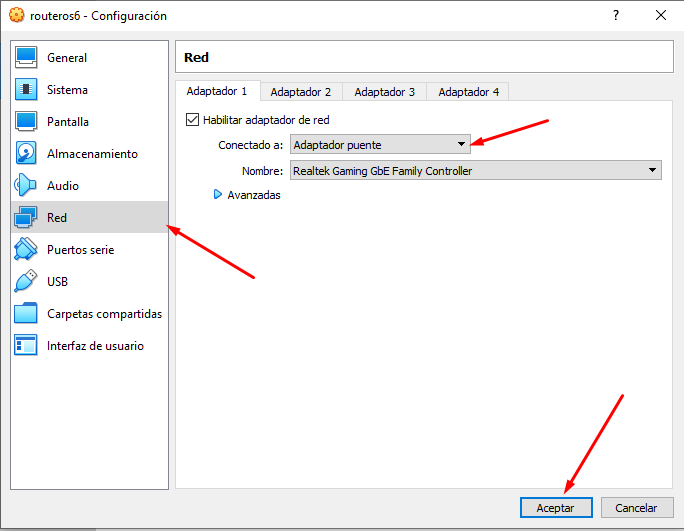](https://docs.zequenze.com/uploads/images/gallery/2022-02/0NlDdNUBWluKZXnU-image-1645541986896.png)
---
## Step 3: Install RouterOS
### Boot and Installation
1. Start the virtual machine
[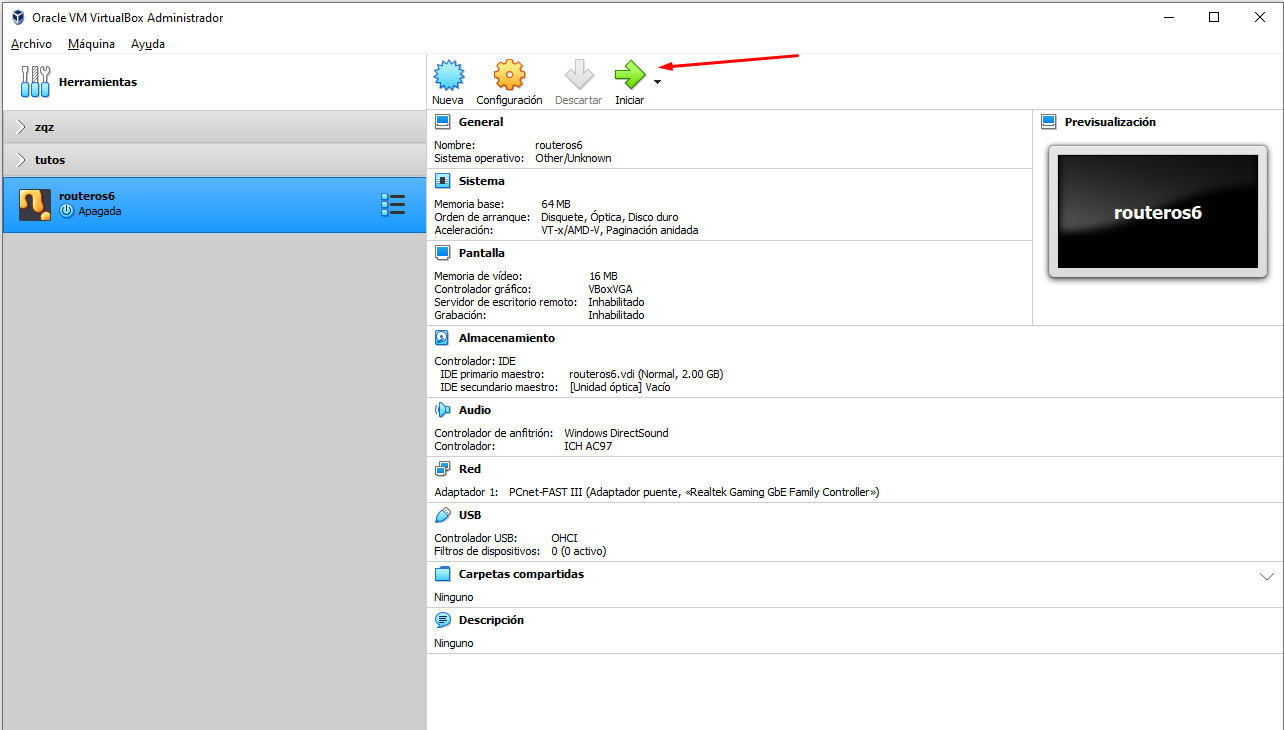](https://docs.zequenze.com/uploads/images/gallery/2022-02/8LfoRYGvfIESust8-image-1645542013174.png)
2. Select the RouterOS ISO image and boot the VM
[](https://docs.zequenze.com/uploads/images/gallery/2022-02/FWlfut4uMtk5LI5V-image-1645542036477.png)
3. When the package selection screen appears, press **A** to select all packages
[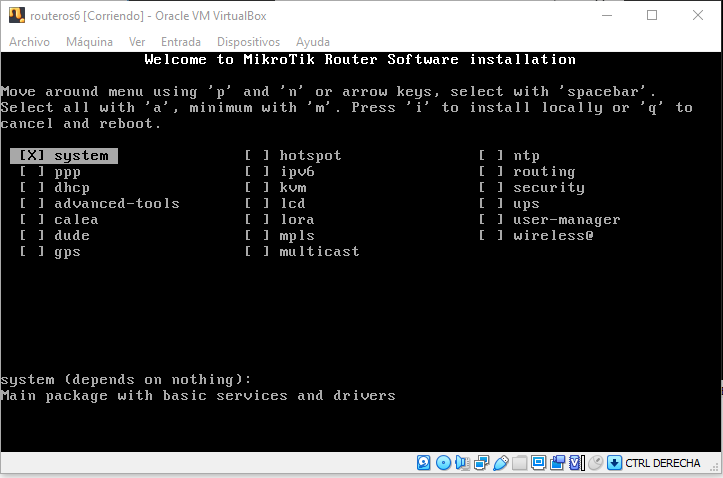](https://docs.zequenze.com/uploads/images/gallery/2022-02/FnaF3ra8nKDGW0iC-image-1645542066394.png)
[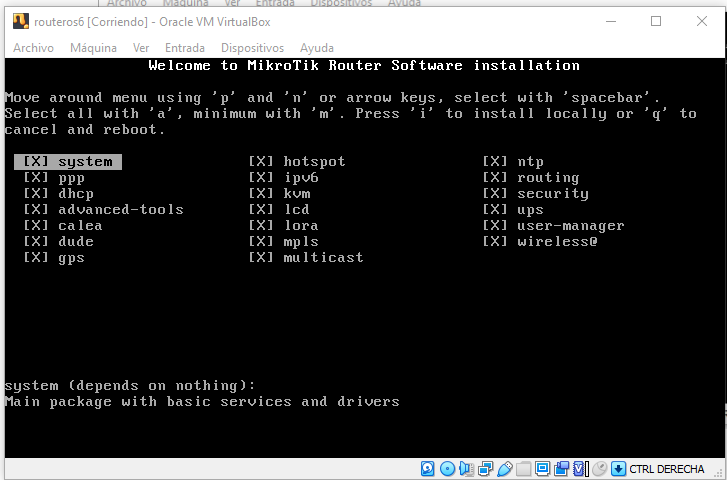](https://docs.zequenze.com/uploads/images/gallery/2022-02/qWZ02CJDJvT9RX7g-image-1645542074001.png)
4. Press **I** to start the installation and confirm when prompted
[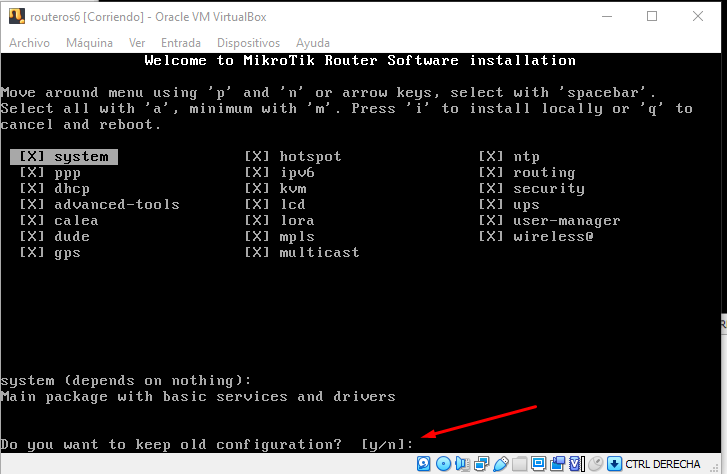](https://docs.zequenze.com/uploads/images/gallery/2022-02/QgDiq5kuy3Orpw0n-image-1645542109056.png)
5. After installation completes, **unmount the ISO image** to prevent the installation wizard from restarting
[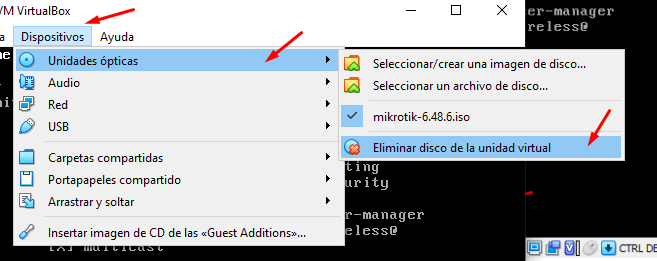](https://docs.zequenze.com/uploads/images/gallery/2022-02/fMhuTbjcDkRs7Sqz-image-1645542125618.png)
---
## Step 4: Initial Configuration
### Login to RouterOS
1. Once the login screen appears, use the default credentials:
- **Username:** `admin`
- **Password:** (leave blank)
[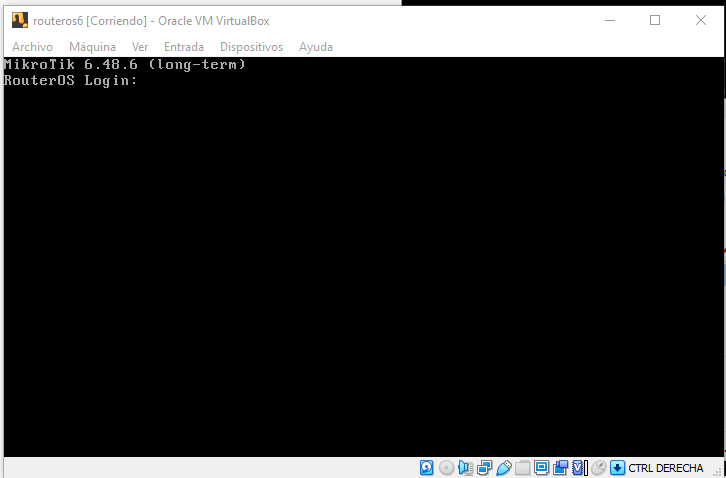](https://docs.zequenze.com/uploads/images/gallery/2022-02/fGdqNyGSOr4oPccn-image-1645542150525.png)
### Assign IP Address
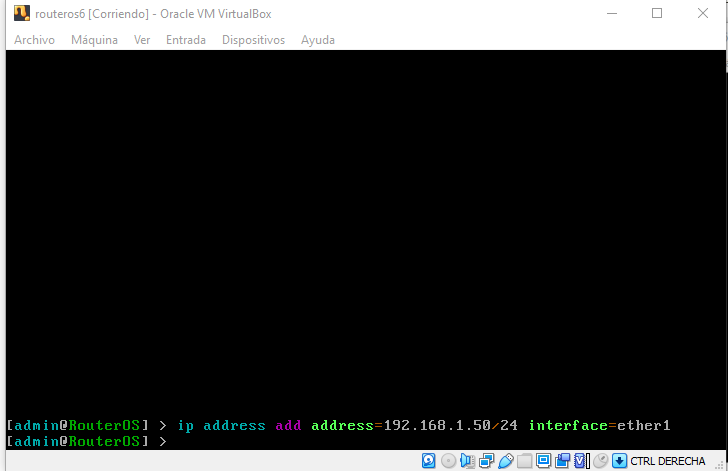
2. Add an IP address to enable remote access. For this example, we'll use `192.168.1.50`:
```
ip address add address=192.168.1.50/24 interface=ether1
```
[](https://docs.zequenze.com/uploads/images/gallery/2022-02/QBpkaJ7zWJ0P0zvw-image-1645563333612.png)
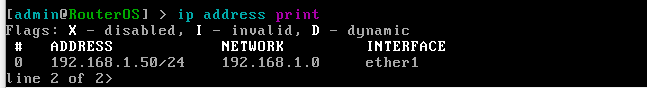
3. Verify the IP address was added correctly:
```
ip address print
```
[](https://docs.zequenze.com/uploads/images/gallery/2022-02/t0QzRo5FoP31CENj-image-1645563369321.png)
### Access Web Interface
4. Open a web browser and navigate to the RouterOS web interface using the IP address you configured:
```
http://192.168.1.50/webfig/
```
[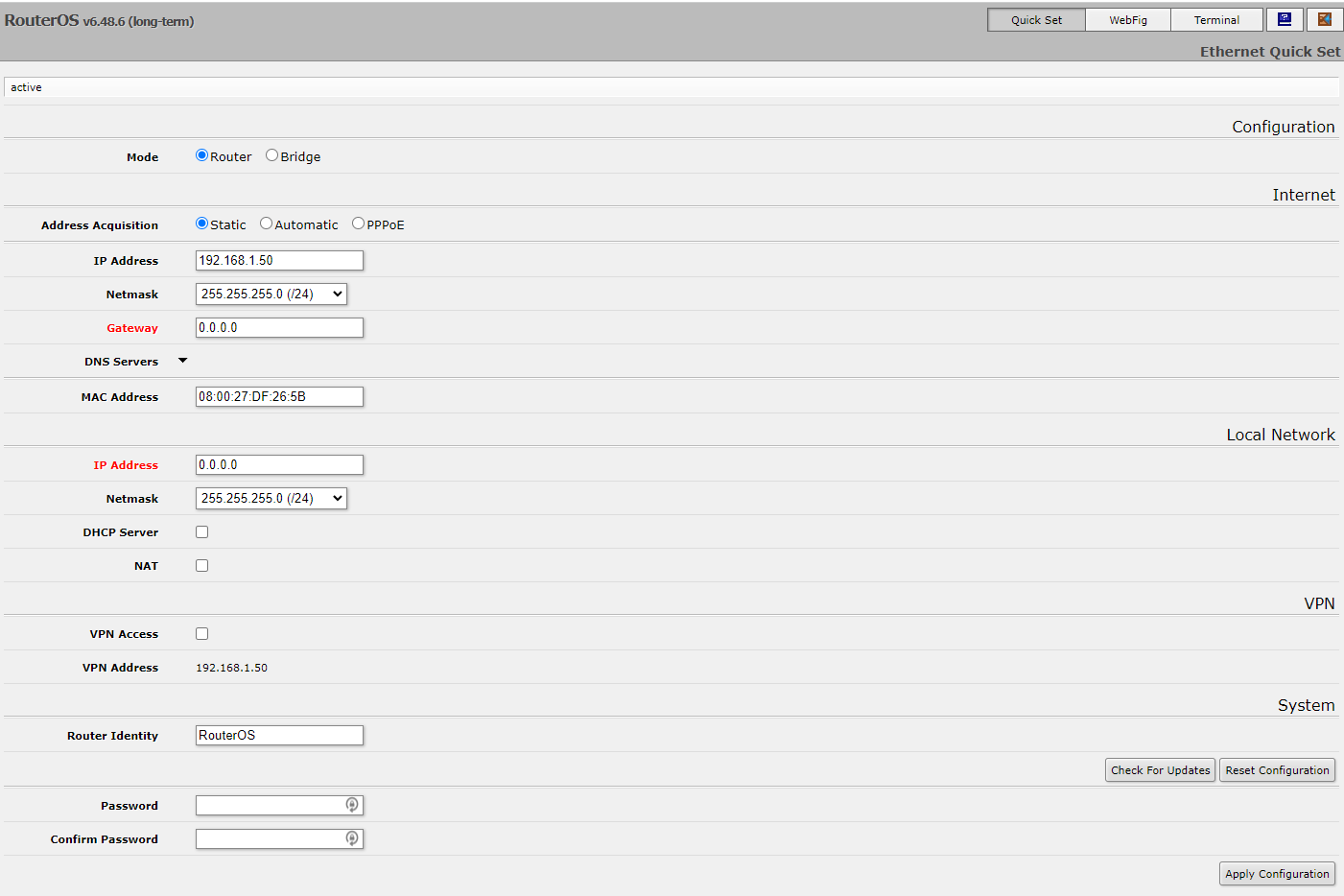](https://docs.zequenze.com/uploads/images/gallery/2022-02/2K0GfMwkPJRwn5IF-image-1645563400046.png)
5. Click on **WebFig** to access the full configuration interface
[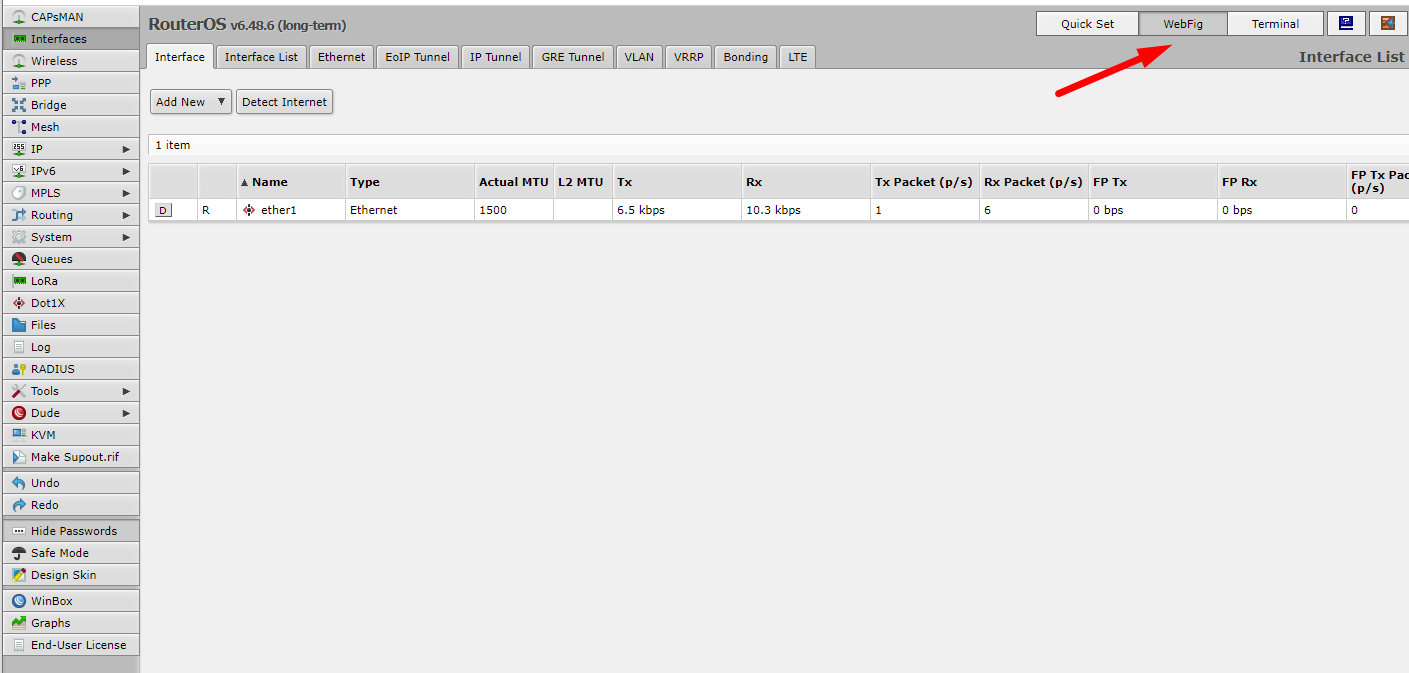](https://docs.zequenze.com/uploads/images/gallery/2022-02/hf41tP5PGFYJZomZ-image-1645563427078.png)
---
## Step 5: Install TR-069 Package
1. Navigate to **Files** in the WebFig interface and upload the TR-069 package
[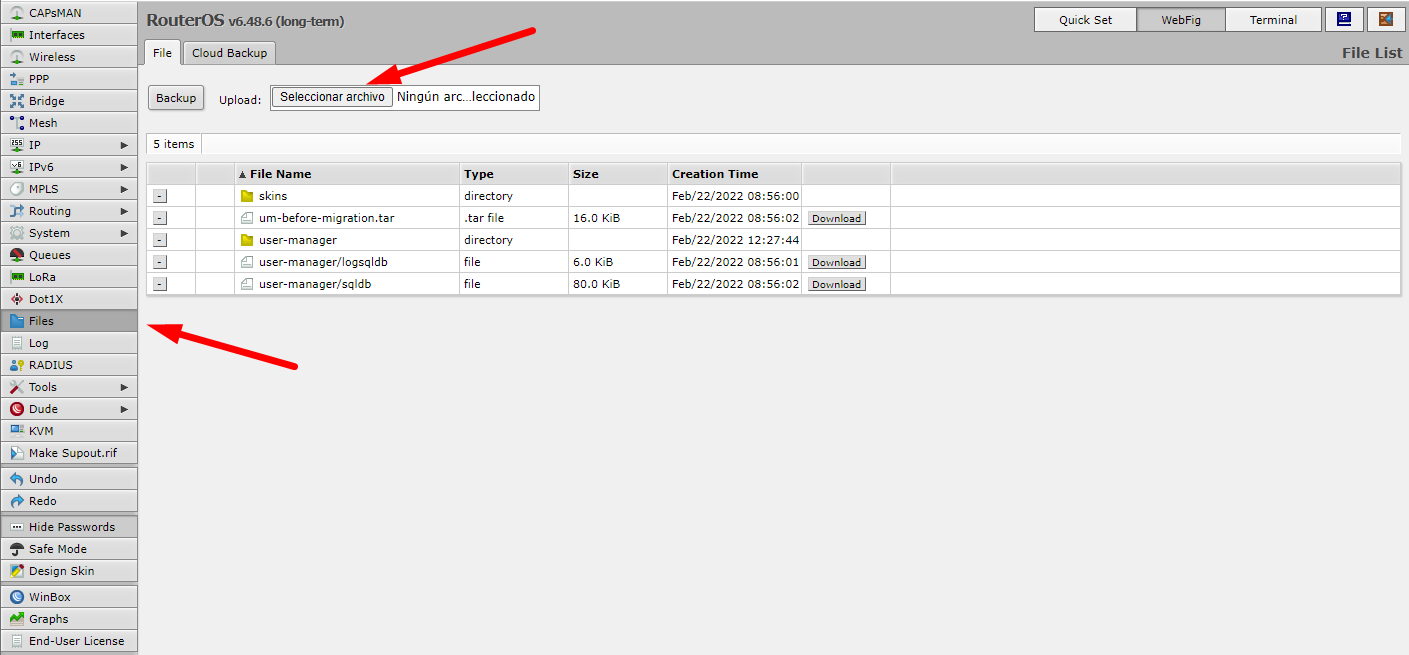](https://docs.zequenze.com/uploads/images/gallery/2022-02/o1VsZ4lB9Z1oPuVq-image-1645563446671.png)
2. Extract the downloaded Extra packages archive and locate the TR-069 package file
[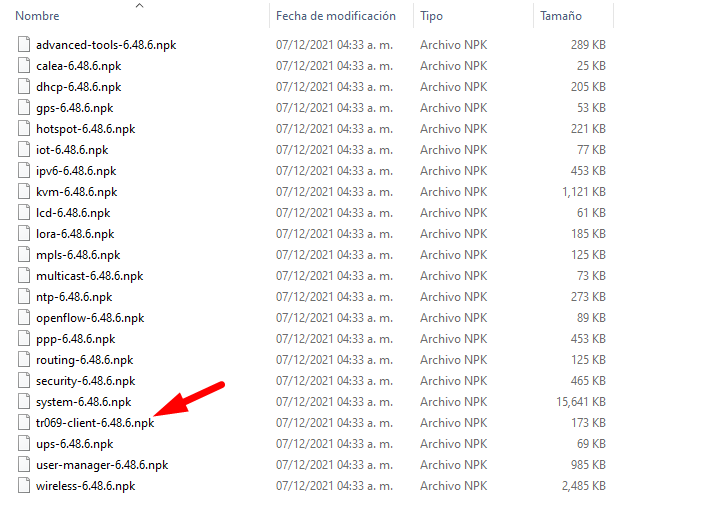](https://docs.zequenze.com/uploads/images/gallery/2022-02/xX4Yt6RhcNyPC9l2-image-1645563471763.png)
[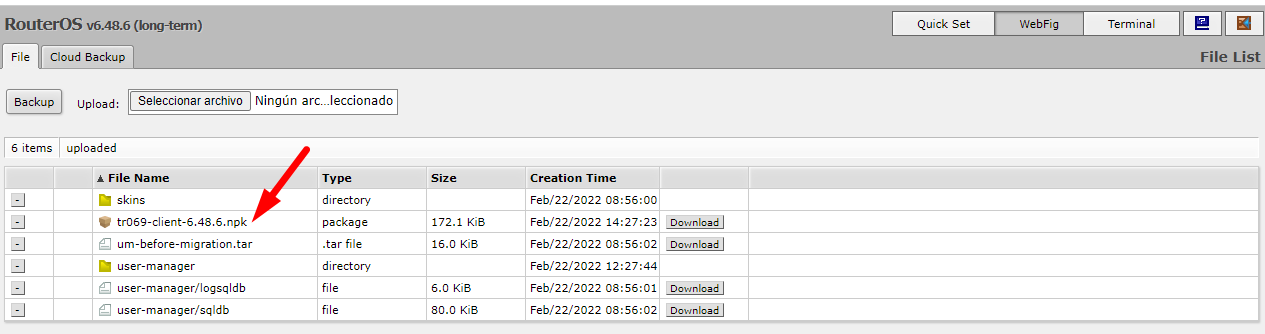](https://docs.zequenze.com/uploads/images/gallery/2022-02/e84Zdqk86j3sQRE7-image-1645563481019.png)
3. Reboot the router to complete the package installation
[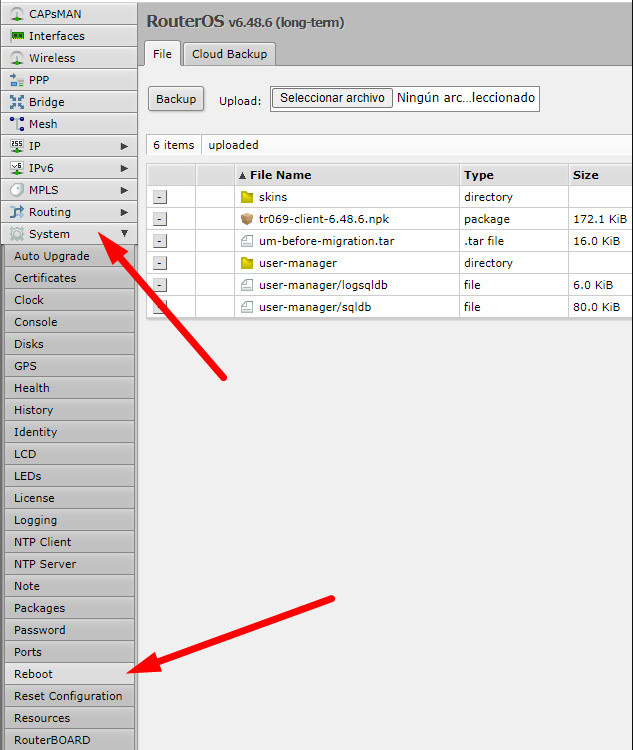](https://docs.zequenze.com/uploads/images/gallery/2022-02/mCKFdZdQrV61gsqO-image-1645563502754.png)
4. After reboot, verify that TR-069 is enabled in the system
[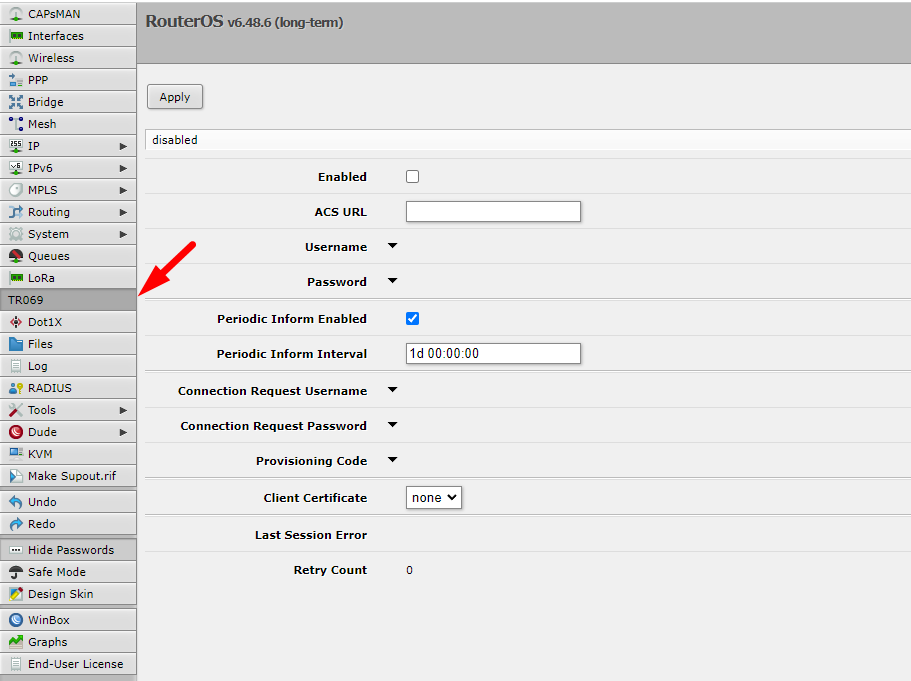](https://docs.zequenze.com/uploads/images/gallery/2022-02/NX3azdMj09hvSmAK-image-1645563525530.png)
---
## Step 6: Obtain RouterOS License
RouterOS displays a warning message indicating you have 24 hours to use the software without a license. You must register to obtain a free demo license.
### Save Software ID
1. Note the **Software ID** displayed in the license warning message
[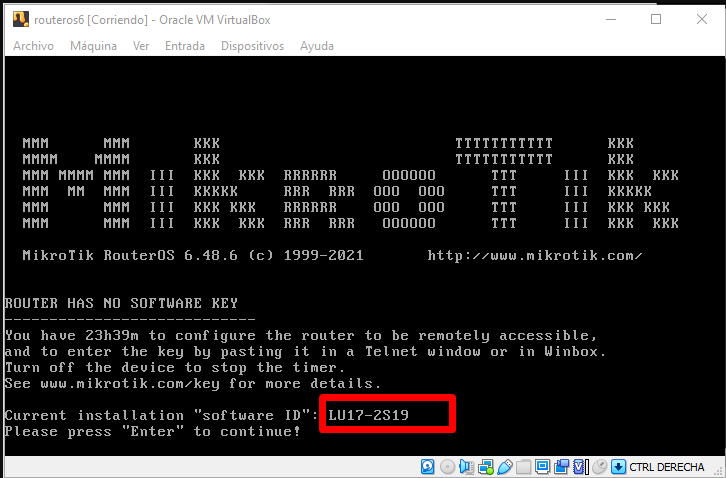](https://docs.zequenze.com/uploads/images/gallery/2022-02/5BvjCyM4Z2Z3NLnE-image-1645563554969.png)
### Generate License Key
2. Register for a MikroTik account at the [registration page](https://mikrotik.com/client/register)
3. After logging in, navigate to **MAKE A DEMO KEY**, enter your Software ID, and generate the license
[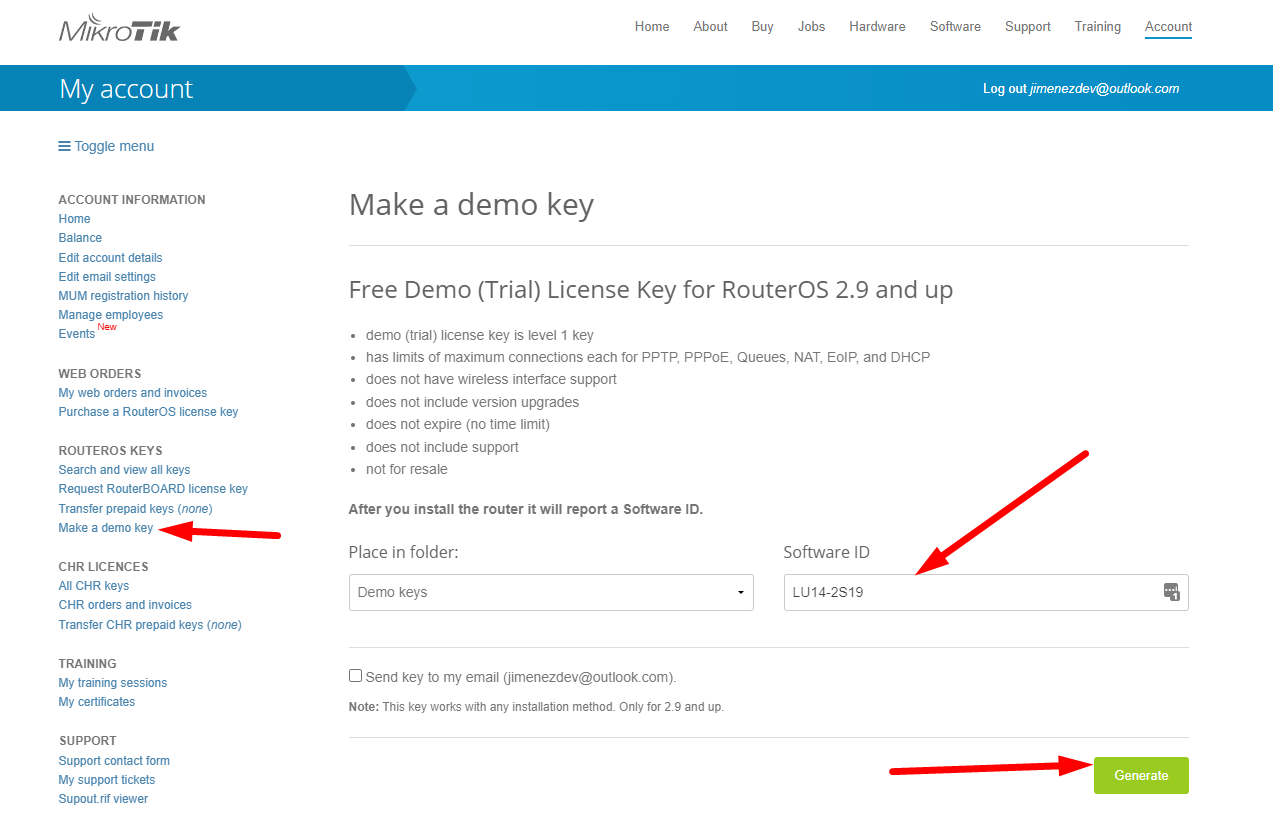](https://docs.zequenze.com/uploads/images/gallery/2022-02/A0Oy5zD3L2m5qXb8-image-1645563588494.png)
[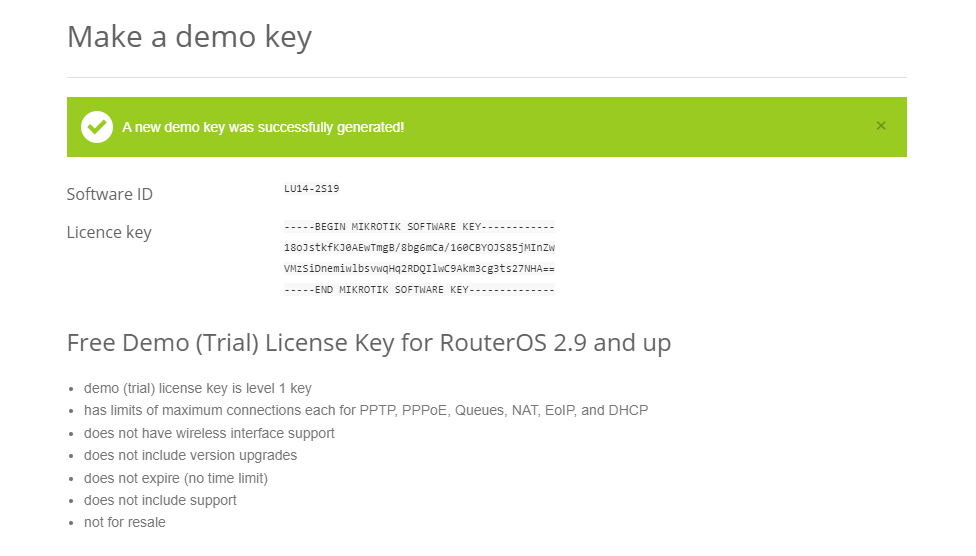](https://docs.zequenze.com/uploads/images/gallery/2022-02/jJPsEw1XviNGVZXf-image-1645563598789.png)
### Activate License
4. Connect to RouterOS via SSH
[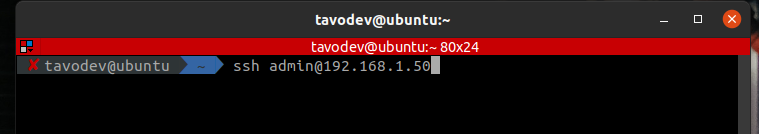](https://docs.zequenze.com/uploads/images/gallery/2022-02/YjhkFhBwsPvc73Jb-image-1645825961461.png)
5. Paste the license key in the terminal and reboot to complete activation
[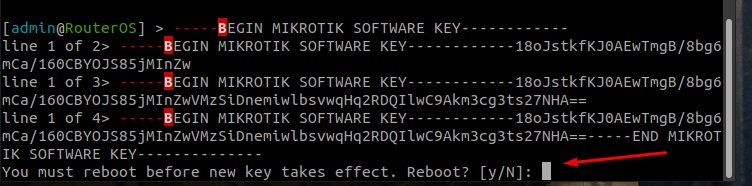](https://docs.zequenze.com/uploads/images/gallery/2022-02/Tu0LgvBlhPYYSxad-image-1645825982230.png)
6. After reboot, a confirmation message indicates the license was successfully activated
[
The profile defines Phase 1 parameters for the IPsec connection.
1. Click the **Profiles** tab in the center panel
2. Click **Add New** to create a new profile
3. Configure the following Phase 1 parameters:
- **Name**: Enter a descriptive name to identify the profile (e.g., "profile-to-ctl01.dev")
- **Hash Algorithms**: Select a hash algorithm that matches the configuration on the remote endpoint
- **Encryption Algorithm**: Choose an encryption algorithm that matches the remote endpoint configuration
- **Lifetime**: Leave the default value (measured in seconds)
- **NAT Traversal**: Enable this option if the router is behind NAT
- **DPD Interval**: Leave the default value for Dead Peer Detection and note this number
- **DPD Maximum Failures**: Leave the default value
4. Click **Apply**, then click **OK**
---
### Step 2: Configure Peers
The peer configuration defines the remote VPN endpoint.
1. Click the **Peers** tab
2. Click **Add New**
3. Configure the following fields:
- **Name**: Enter a name to identify the remote peer
- **Address**: Enter the remote public IP address (e.g., 35.35.35.22/32)
- **Profile**: Select the profile created in Step 1
- **Exchange Mode**: Select the exchange mode (IKE2 is recommended)
4. Click **Apply**, then click **OK**
---
### Step 3: Configure Identities
The identities configuration defines authentication credentials.
1. Click the **Identities** tab
2. Click **Add New**
3. Configure the following fields:
- **Peer**: Select the peer configured in Step 2
- **Auth. Method**: Select "pre shared key"
- **Secret**: Enter the pre-shared key that will be configured on both endpoints
4. Click **Apply**, then click **OK**
---
### Step 4: Configure Proposals (Phase 2)
The proposal defines Phase 2 parameters for the IPsec connection.
1. Click the **Proposals** tab
2. Click **Add New**
3. Configure the following Phase 2 parameters:
- **Name**: Enter a name to identify this proposal
- **Auth. Algorithms**: Select the authentication algorithm to be used on both endpoints
- **Encr. Algorithms**: Select the encryption algorithm to be used on both endpoints
- **Lifetime**: Set the lifetime for Phase 2
- **PFS Group**: Select the Diffie-Hellman group for Perfect Forward Secrecy (PFS). This determines the session key generation during key exchange
4. Click **Apply**, then click **OK**
---
### Step 5: Configure Policies
The policy defines which traffic should pass through the VPN tunnel.
1. Click the **Policies** tab
2. Click **Add New**
3. Configure the following fields:
- **Peer**: Select the peer configured in Step 2
- **Tunnel**: Enable this option to establish the tunnel between both sites
- **Src. Address**: Enter the local IP address or network that will pass through the tunnel
- **Dst. Address**: Enter the remote IP address or network that will be received from the other end
- **Level**: Select "unique"
- **Proposal**: Select the proposal created in Step 4
4. Click **Apply**, then click **OK**
---
## Part 2: CONTROL Configuration
### Initial Navigation
1. Navigate to the **Links** section in the left-side menu
2. Select the **Services** tab at the top
3. Click the **+Add** button
---
### Step 1: Create IPsec Security Service (Phase 1)
1. Configure the basic information:
- **Name**: Enter a name to identify Phase 1
- **Short-name/code**: Enter a short identifier for quick reference
- **Organization**: Select the organization that will use this connection
- **Type**: Select "IPsec Security"
2. Click **Save** at the bottom
3. Configure the Phase 1 parameters to match your RouterOS configuration:
- **Authentication method**: Select "PSK"
- **IKE version**: Select "Version 2"
- **Encryption algorithm**: Enter "aes256"
- **Integrity algorithm**: Enter "sha256" or "sha2_256"
- **Diffie Hellman group (PFS)**: Enter "modp1024"
- **Lifetime**: Enter 1200 (equivalent to 20 minutes)
- **Key negotiation retries**: Enter "0"
- **Aggressive Mode**: Enable this option
4. Click **Save and close** at the bottom
---
### Step 2: Create IPsec Configuration Service (Phase 2)
1. In the **Services** tab, click **+Add** again to create another service
2. Configure the basic information:
- **Name**: Enter a name to identify Phase 2
- **Short-name/code**: Enter a short identifier for quick reference
- **Organization**: Select the organization that will use this connection
- **Type**: Select "IPsec Configuration"
3. Configure the Phase 2 parameters to match your RouterOS configuration:
- **Tunnel type**: Select "Tunnel (ESP)"
- **Encryption algorithm**: Enter "aes256"
- **Integrity algorithm**: Enter "sha256" or "sha2_256"
- **Diffie Hellman group (PFS)**: Enter "modp1024"
- **Lifetime**: Enter 1200 (equivalent to 20 minutes)
---
### Step 3: Create Association
1. In the **Links** section, select the **Association** tab
2. Click the **+Add** button
3. Configure the following fields:
- **Name**: Enter a name to identify this association
- **Short-name / code**: Enter a short identifier for quick reference
- **Type**: Leave "IPSec VPN" selected
- **Local gateway type**: Leave "Private IP" selected
- **Remote gateway address**: Enter the remote public IP address you are connecting to
- **Remote gateway id**: Enter the WAN interface IP of the RouterOS device
- **Secret**: Enter the pre-shared key (must match the secret configured in RouterOS)
- **Security service**: Select the IPsec Security service created in Step 1
- **Configuration service**: Select the IPsec Configuration service created in Step 2
- **Server**: Select the internal server to use
- **Organization**: Select the organization that will use this connection
---
### Step 4: Create Link
1. In the **Links** section, ensure you are on the **Links** tab
2. Click the **+Add** button
3. Configure the following fields:
- **Name**: Enter a name to identify this link
- **Short-name / code**: Enter a short identifier
- **Active**: Enable this option to activate the link
- **Association**: Select the association created in Step 3
- **Local network**: Enter the local Zequenze IP address
- For CONTROL: typically `172.31.255.254/32`
- For GATE: typically `172.31.255.253/32`
- (Verify the correct IP internally before configuring)
- **Remote network**: Enter the remote network or IP address that will pass through the tunnel to Zequenze
- **Check services**: Select "PING Connectivity test" to validate tunnel communication
- **Check address/hostname**: Enter a remote IP address that is always active for connectivity testing (typically the remote gateway, e.g., 192.168.106.154)
- **Organization**: Select the organization that will use this VPN connectivity
---
## Verification and Summary
### RouterOS Connection Status
Once the configuration is complete, you should see the connection established in RouterOS as shown below:
### CONTROL Connection Status
The Link within CONTROL should appear as follows when successfully established:
This completes the IPsec VPN tunnel configuration between RouterOS and CONTROL. The tunnel should now be active and passing traffic between the configured networks.
# Setting up TR-069 client on mikrotik hAP ac2
## Prerequisites
Before configuring the TR-069 client, ensure your MikroTik hAP ac2 device has an active internet connection.
## Required Configuration Parameters
You will need the following credentials and settings to configure the TR-069 client in CONTROL:
- **ACS URL:** The endpoint URL where your device will report its status and receive management commands
- **Username:** Authentication username for the ACS URL
- **Password:** Authentication password for the ACS URL
> **Note:** These credentials should be provided by your CONTROL administrator or obtained from your CONTROL portal settings.
## Configuration Steps
Follow the video tutorial below for step-by-step instructions on configuring the TR-069 client on your MikroTik hAP ac2:
## Additional Information
The TR-069 protocol enables remote management and monitoring of your MikroTik device through the CONTROL platform. Once configured, your device will automatically establish communication with the ACS server and appear in your CONTROL dashboard.